Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Four Square Cipher
The four-square cipher is a manual symmetric encryption technique which utilizes four 5×5 matrices of letters arranged in a square. Each of these 5×5 squares contain all of the letters of the alphabet, though leaving out the letter Q to bring it down to fit in 25 characters. The plaintext is split into Digraphs (pairs of two letters) and then encrypted using a method similar to the Playfair Cipher.
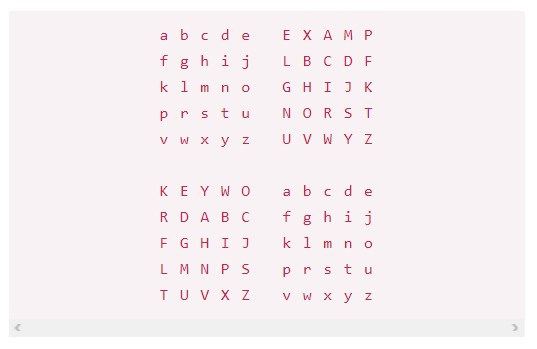
First, we need to create our four squares. The top left and bottom right squares will have just the alphabet (minus Q) in order left to right. The other two squares will have our two (not one, but two) keywords (passwords), dropping any duplicate letters, followed by the rest of the letters of the alphabet in alphabetical order. The end result is four squares, each with all 25 letters of the Q-less alphabet.

Now that we have our key tables, we can encrypt a message. Let’s say we want to encrypt the words “three fifty”.
We first must split the plaintext into digraphs (pairs of two letters) such as follows: “TH RE EF IF TY”. If there was an odd number of letters, we’d simply add a Z at the end to have complete digraphs. To encrypt each digraph, we will first match the two letters to the first and fourth squares that we have, in this case matching T and H:
Then, using the other two squares, we find where they would intersect with the other two tables if they were to form a rectangle. In this example, T becomes B, and H becomes A.
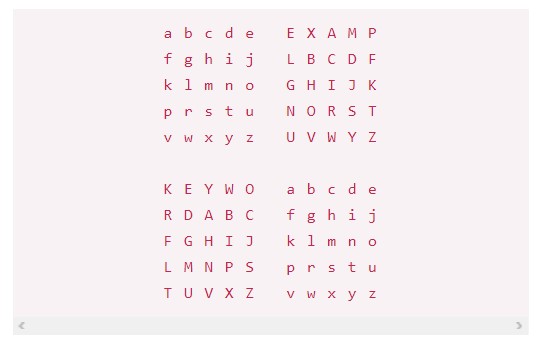
Our first digraph would then encrypt to RB – taking the letter from the horizontally opposing table. Through this simple process, we can encrypt the entire message digraph by digraph.
Decrypting messages encrypted with a four-square cipher is as simple as doing the process in reverse. Assuming you have the keys, you can recreate the tables, which means you can do the same process in reverse for each digraph.
In comparison to other lists of classical ciphers such as Playfair, four-square is much more secure but also much more complicated to use by hand. Due to it’s use of two keys and the extra time required to prepare the four tables, the Playfair cipher was more commonly used as it was easier to work with, despite being less secure.



