Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Transposition Ciphers
Unlike a simple substitution cipher (such as the Caesar Cipher), which switches the letters of a message around, Transposition Ciphers instead work by messing with the order of the letters to hide the message being sent. You can think of this in a way similar to an anagram, but with a more set structure so it can be decrypted easily if you know how it was encrypted.
An excellent example of a Transposition Cipher is Columnar Transposition. For this, we’ll take a message (plaintext) and arrange it into a few columns. Let’s try the phrase “WE ARE DISCOVERED FLEE AT ONCE” – and add a bit of padding (random characters) to the end to make each column equal.
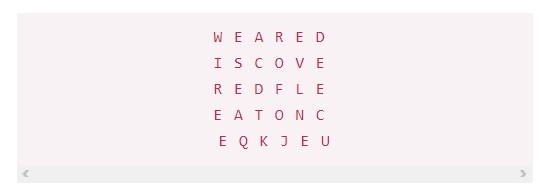
Now, we would take each column vertically to create the ciphertext.
WIth this we’ve arrived at a relatively secure ciphertext. In order to decrypt and read the message, there’s two options: Either read through the message letter by letter (skipping to the next word, etc) or rearrange the letters into the columns. The key in this case would be how many columns there are and how many letters fit into each column. With that information in hand, decrypting this message is easy.
Another example of a transposition cipher is something called a Rail Fence cipher.
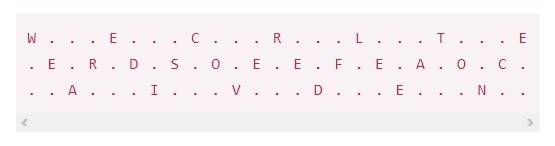
If you look carefully here, you can see the message quite easily. This transposition cipher offers barely any encryption, and is almost a word search (if you were to replace the periods with other letters).
That’s more of less what transposition ciphers are – clever ways of hiding the message your trying to send, sometimes with some type of ‘key’ to allow easier reading. Despite being able to be discovered under some careful consideration, transposition ciphers were popularly used for message sending up until around the 1950’s – eventually methods for breaking them became too well known, as they relied more on the secrecy of their methods rather than their methods themselves.



